GCube Security Model
This page describes the overall security model of gCube. Firstly, the authentication handling is introduced, briefly describing the model and components used by gCube to verify user's identity. Secondly, the authorization section gives a brief description of how the access control is managed in gCube, also introducing main services and components in charge to maintain and enforce authorization policies.
Contents
Authentication
"Authentication is the act of establishing or confirming something (or someone) as authentic, that is, that claims made by or about the subject are true. This might involve confirming the identity of a person, the origins of an artifact, or assuring that a computer program is a trusted one."[1]
Being gCube a distributed system, the authentication process mainly focuses on verifying the identity of communicating entities, i.e. users (through the gCube portal), and Running Instances. This is achieved through the use of authentication tokens, i.e. piece of information, that are exchanged between communicating entities to prove their mutual identity.
Delegation
"In numerous applications it is sometimes necessary to "become" some one else, or some other principal in order to take advantage of some privilege(s) they have. Unix systems have had this concept for decades in the su command. With the advent of web based enterprise applications it became clear that something similar was needed for them. That is it became necessary to be able to pass around a set of privileges in some manner. Since privileges are normally associated with a principal (very often a person) the problem became a question of how to pass around these principal's identities and how to allow one system to use that identity to gain access to information on another system."[2]
In analogy to the previous description, identity delegation in gCube refers to the process of allowing system services and resources to act on user's behalf. This functionality is often required in N-tier multi-domain systems. An important point concerning delegation is that, in gCube, services can be dynamically deployed, and autonomously operate in the infrastructure. This implies that a delegation mechanism of user's credentials is required by those services that act in the infrastructure on the user's behalf.
Model
gCube architecture exploits the Public Key Infrastructure[3] (PKI) to uniquely identify users and services in the infrastructure. gCube users and services are provided with an authentication token, named credentials, i.e. a private key and a public certificate, that are used to authenticate them to other entities. In PKI, credentials are issued and revoked to users by a trusted entity, named Certification Authority (CA). The gCube infrastructure is designed to support CAs acknowledged by the International Grid Trust Federation[4] (IGTF) as well as an infrastructure-specific CA, named "D4Science CA" in the following.
As from the previous, each interaction between gCube Running Instances, e.g. a service invocation, should be performed in gCube using valid credentials, issued by a trusted Certification Authority (CA).
As a consequence of this every authenticated communication between gCube entities is performed using valid credentials, issued by a trusted Certification Authority (CA). As far as the security protocol used during the communication, gCube adopts the HTTPS[5] one. This mechanism provides integrity and privacy, by means of encryption, for authenticated communications. The choice of the HTTPS mechanism to protect gCube interactions, in place of message-level mechanisms like WS-SecureMessage and WS-SecureConversation[6], is mainly due to the better performances provided by HTTPS with respect to message-level security mechanisms.
Nevertheless, despite HTTPS performances, security does not come for free. Sometimes, the overhead introduced in service invocation by the security handshake can take much longer than the invocation itself, thus excessively penalizing the service usability. For this reason, wherever the cost of security was judged too high with respect to advantages introduced, unauthenticated invocations among gCube entities have been allowed also. In those cases, as unauthenticated invocations are performed without valid credentials, neither authentication nor authorization are enforced.
Components
Credentials in the gCube infrastructure are managed by the following set of components:
- MyProxy service - the MyProxy[7] service is in charge of maintaining a delegated short-term copy of user's credentials. The gCube MyProxy configuration allows for storing both credentials issued by IGTF CAs, both for credentials issued by the D4Science CA. In this second case short-lived credentials are generated on the fly for the user, using the MyProxy online CA functionality[8].
- Delegation and CredentialRenewal services - The Delegation service is in charge to provide gCube services with valid credentials to authenticate themselves in the infrastructure. The provisioning of credentials to services operated by the Delegation depends on service security configuration, being the use of container credentials the most common, and simple, case. For services requiring to act on the user behalf, the Delegation interacts with the Credentials Renewal service and retrieve user's credentials, under a set of predefined delegation policies.
A more detailed description of the structure and behaviour of the authentication-related components can be found in the Virtual Organisation Management page.
Authorization
"Authorization is the function of specifying access rights to resources, which is related to information security and computer security in general and to access control in particular. More formally, "to authorize" is to define access policy. For example, HR staff are normally authorized to access employee records, and this policy is usually formalized as access control rules in a computer system. During operation, the system uses the access control rules to decide whether access requests from (authenticated) consumers shall be granted or rejected."[9].
Authorization rights in gCube are modeled basing on the RBAC[10] model. In such a model each user must held a role to operate in the gCube infrastructure. In particular authorization policies in the system are defined with respect to roles, that, in turn, are assigned to users. Each resource is then in charge to enforce authorization policies on incoming requests.
In distributed multidomain systems the concept of VO is the base to create virtual environments spanning across different administrative domains[11]. gCube architecture mainly aims at enabling Virtual Research Environments, and for this reason Virtual Organizations are a core concept of GCube. In particular, when it comes to authorization, the RBAC model must be merged to the sharing of resources typically enabled by VOs.
Model
Policies granting access to resources complies with the following gCube VO authorization model. In particular authorisation policies are scope specific, being the scope defined as from the gCube reference model [12]. It is worth noticing that the scope introduced in the gCube reference model corresponds to the VO element in the following model.
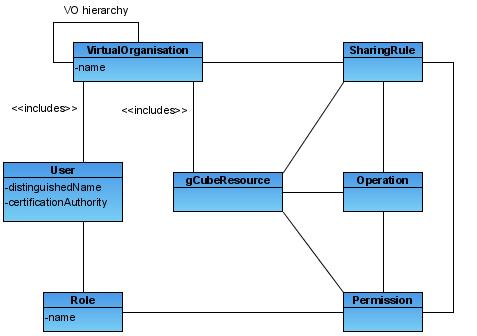
Each element in the diagram is briefly introduced below:
- VO: Each VO in the hierarchy represent a context in which authorization rights can be defined and must be evaluated (Scope). Users and Resources can be included in multiple VOs. Sharing rules can be defined by Resource Managers w.r.t. entire VOs.
- User: Users of the gCube system. This definition includes every service and agent able to autonomously act in the infrastructure. Every user will be univocally identified using a set of user credentials as described in the previous Authentication section.
- Resource: This element represents all gCube resources. Each resource is identified through a resource id. Resources have to belong to a resource type.
- ResourceType: Resource types divides resources in different partitions. Each Resource type is associated to a set of logical operations. These operations can be performed over resources of that type.
- Operation: These are logical operations supported by resources of a given type. Sharing rules and Permissions can be defined using these operations.
- Sharing Rule: Resource Managers can grant VO members access to a given resource defining sharing rules. Sharing rules applies to entire VO, while Permissions applies to roles in a specific VO.
- Permission: Permissions can be defined by VO Managers to grant the right to perform operations to a given role.
- Role: Roles are associated to users in order to give them permissions to execute a set of operations. Role are hierarchical, child roles inherit permissions of parent roles. Hierarchy allows multiple inheritance. Inheritance relationship among roles can be defined only at role creation.
Policy enforcement requires resources to contact authorization components, described below, to verify if incoming requests complies with the set of defined policies. The push authorization model is used to enforce authorization for gCube resources[13]. In such a model a piece of information containing the role assignment, and signed by a trusted identity, is embedded in the client certificate, and send to the service during authentication[[14]]. Resources can thus extract user roles from the received certificate and, knowing the resource id, the scope, and the operation invoked, contact the authorization components to get an authorization decision.
Components
Following main elements are part of the gCube authorization architecture:
- VOMS - A VOMS[15] server maintains the scope hierarchy as a VOMS groups hierarchy. It is also in charge to store the set of gCube users, as well as their group membership and roles assigned to them. This component is also in charge to sign
- Resource Authorization Service - This service is in charge to store authorization policies for gCube resources, i.e. which roles are needed in a given VO to perform an operation on a resource. This component is also in charge of issuing authorization decisions, whenever asked by resources itself. Multiple instances of the authorization service are usually deployed in the infrastructure to avoid bottleneck in policy evaluation.
A typical usage scenario for GCube, involving authentication and authorization functionalities is shown in the following diagram.
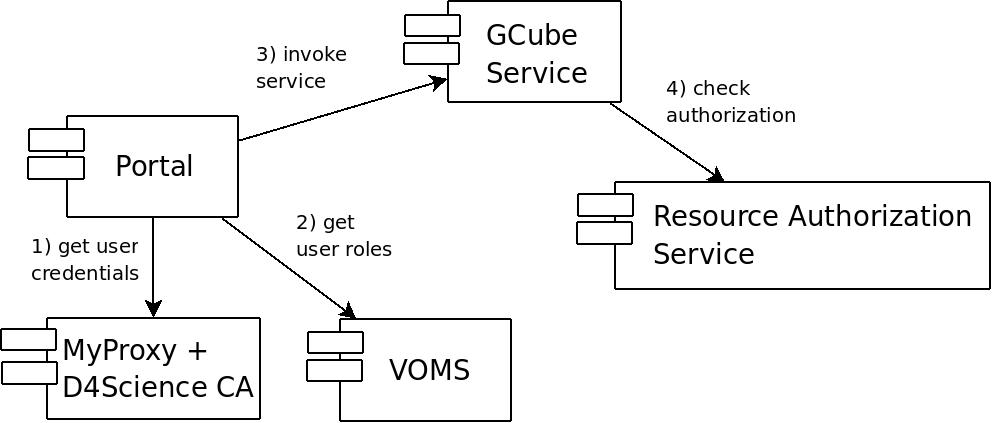
- When the user logs in the portal, credentials associated with her username/password are retrieved from the MyProxy repository.
- The user is then asked to select the VRE where she wants to operate. The selection triggers the enrichment of user credentials with an attribute certificate signed by the VOMS server. The attribute certificate contains roles held by the user in the current VRE. The credentials obtained are stored in the user session. The user can always change the VRE selection later on; in this case fresh credentials will be generated for the newly selected VRE.
- During the user session, a number of service invocations happens from the portal to backend services. These invocations are performed with user credentials, enriched with user roles, created in the previous step. On the gCube service side the invocation is authenticated, validating user credentials, and authorized, contacting the Resource Authorization Service.
References
- ↑ http://en.wikipedia.org/wiki/Authentication
- ↑ http://middleware.internet2.edu/webiso/docs/draft-lajoie-trust_and_delegation-02.html
- ↑ http://en.wikipedia.org/wiki/Public_key_infrastructure
- ↑ http://www.igtf.net/
- ↑ http://en.wikipedia.org/wiki/HTTP_Secure
- ↑ http://specs.xmlsoap.org/ws/2005/02/sc/WS-SecureConversation.pdf
- ↑ http://grid.ncsa.uiuc.edu/myproxy/
- ↑ http://grid.ncsa.uiuc.edu/myproxy/ca/
- ↑ http://en.wikipedia.org/wiki/Authorization
- ↑ http://en.wikipedia.org/wiki/Role-Based_Access_Control
- ↑ http://www.ci.uchicago.edu/events/VirtOrg2008/VO_report.pdf
- ↑ https://technical.wiki.d4science.research-infrastructures.eu/documentation/index.php/Reference_Model
- ↑ http://www.ogf.org/documents/GFD.38.pdf
- ↑ http://www.ietf.org/rfc/rfc3281.txt
- ↑ http://grid-auth.infn.it/