User Security
Security Basics
Basics of User Security. Digital Certificates, CAs etc. Authorization and Authentication procedures
The DILIGENT Security model uses Public Key Infrastructure (PKI) mechanisms to authenticate identities acting in the infrastructure.
Each authenticated invocation must be performed using valid credentials issued by a trusted Certification Authority (CA).
Acquiring a Digital Certificate
The standard procedure for acquiring a Digital Certificate from the appropriate accredited Certification Authority is based on a certain number of steps.
First of all users has to request a CA certificate and to install it on his browser. CA policy requests that in your institute a Registration Authority (RA) is defined. A Registration Authority is a person responsible to identify user for CA.
Second needed step is request a digital certificate to a local Registration Authority. The Registration Authority will start a simple procedure and will give to user an ID. After receiving this ID, user can compile his personal data for CA. The ID verifies them. Then user's browser will ask him for a password: this password is used to the encrypt the private key before saving it locally.
The browser will generate the couple of private-public and it will send your public key to the CA to be signed. Typically in a few days user will receive an email from CA with an URL.
It is necessary use the same browser and the same machine used to generate the couple private-public key to connect to that URL. The browser will install the certificate (i.e. your public key signed by CA) and user will be prompted for the password to access to the private key. At this point the certificate plus your private key are saved encrypted on the configuration files of your web browser.
This certifcate can be exported on your filesystem as backup.
Accessing a Community Portal
DILIGENT infrastructure is able to provide credentials to user without a personal certificate. These credentials are generated in a transparently way for the user through the DILIGENT Portal.
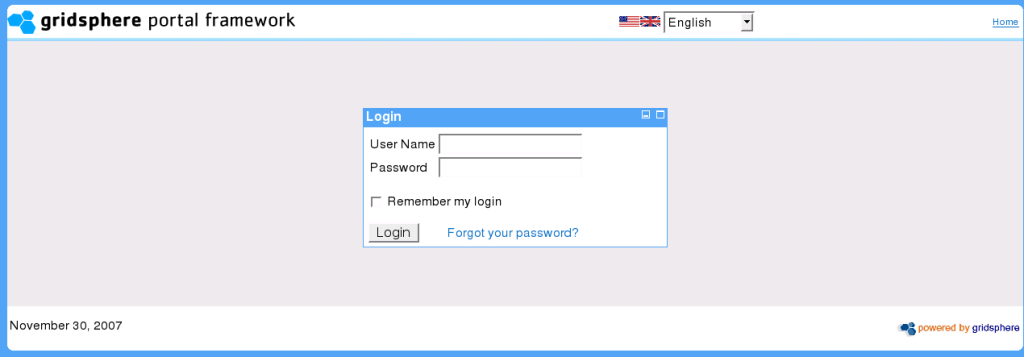
In particular DILIGENT portal login phase is subdivided in two main steps:
- Insert UserName and Password
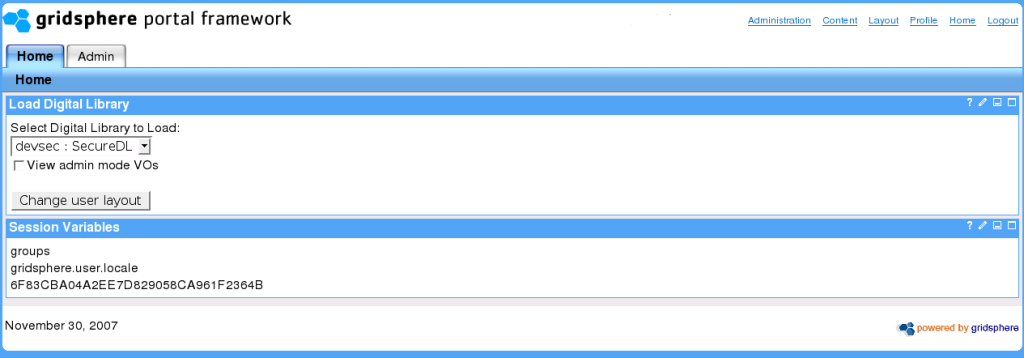
- Specify the DIGITAL LIBRARIES to load. This choice will affect also the available credentials for the user during the session.
In this way the user inherits all the privileges he has in terms of group membership and roles in DILIGENT VOMS.