Difference between revisions of "Auth Portlet"
(→Insert a Policy) |
(→Insert/Modify a Policy) |
||
| (42 intermediate revisions by 2 users not shown) | |||
| Line 5: | Line 5: | ||
==Introduction== | ==Introduction== | ||
| + | With this portlet it’s possible to create a policy to deny access for a user or group of users to a service or group of services in a specific context. | ||
| − | + | ''Below it is shown the overall layout of the Auth Portlet'' | |
| − | + | [[Image:AuthPortlet_List_Detail.png|80%|center|Auth Portlet Overall]] | |
| + | Every policy is consisting of: | ||
| + | #one or more Caller | ||
| + | #Service | ||
| + | #Access | ||
| − | [[Image: | + | |
| + | '''The caller''' can be an User, a Role or a Service and you can insert one or more callers for each policy. | ||
| + | |||
| + | ''(The insertion of a policy with more callers results as more policy).'' | ||
| + | |||
| + | '''The service ''' is specified as service class, service name and service id. | ||
| + | |||
| + | '''The access ''' that we want to deny can be: | ||
| + | |||
| + | *All | ||
| + | *Access | ||
| + | *Delete | ||
| + | *Execute | ||
| + | *Write | ||
| + | |||
| + | ==Insert/Modify a Policy== | ||
| + | |||
| + | For insert a policy we can add one or more Caller, one service and access type. | ||
| + | |||
| + | The insertion of a caller can be made with an autocomplete writing in the input, or clicking the button Add User role or add service, that opens a pop-up to insert more things. | ||
| + | |||
| + | We can create a policy that inserts all users or all role with the specific button “All Users” or “All Role” | ||
| + | |||
| + | The insertion of a caller can be made with complete input text , or clicking button “Add User/ Role” or “Add Service” to open a pop up for multiple entry. | ||
| + | |||
| + | The insertion with an autocomplete can be made with the insertion of a first controlled character: | ||
| + | |||
| + | *if you insert a user, you can digit @ for see all users | ||
| + | *if you insert a role, you can digit # for see all roles | ||
| + | *if you want insert a service, you can digit $ for see all the services. | ||
| + | |||
| + | |||
| + | [[Image:AuthPortlet_InsertPopUp.png|100%|center|Auth Portlet Insert a Policy]] | ||
| + | |||
| + | The selection of the service and the access type It’s done with a selected dropdown | ||
| + | |||
| + | We can insert a policy that allows the use of a service only to one or more caller, selecting the combination ALL Users/All role and Except. | ||
| + | |||
| + | In this case, the callers, entered in input text, are enabled to access a service. | ||
| + | |||
| + | For an existing policy, you can change only the service and the access type. | ||
==Search a Policy== | ==Search a Policy== | ||
| + | It Is possible to search, filter and group by all policy. | ||
| + | |||
| + | |||
| + | [[Image:AuthPortlet_Filter_detail.png|100%|center|Auth Portlet Filter a Policy]] | ||
| + | |||
| + | |||
| + | [[Image:AuthPortlet_Filter_bar.png|300px|center|Auth Portlet Search a Policy]] | ||
| + | |||
| + | If we want to search a caller, we can digit @ before inserting a name of the caller. | ||
| + | |||
| + | If we want to search a service, we can digit $ before inserting a name of the service. | ||
| + | |||
| + | And finally if we want to search an access, we can digit * before inserting a type of an access. | ||
| + | |||
| + | The filter can be incremental. | ||
| + | |||
| + | |||
| + | [[Image:AuthPortlet_Filter_search.png|800px|center|Auth Portlet Search a Policy]] | ||
| + | |||
| + | |||
| + | Over the filter we can organize a policy in caller type, for example user, role and service | ||
| + | |||
| + | [[Image:AuthPortlet_Filter_group.png|200px|center|Auth Portlet Group a Policy]] | ||
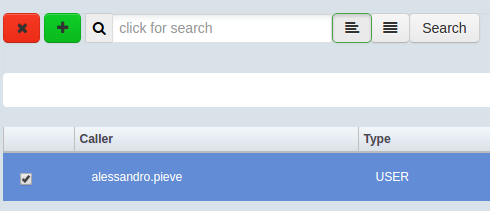
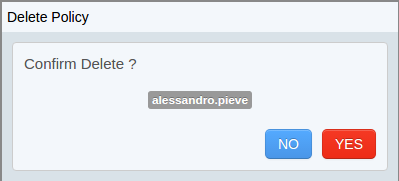
==Delete a Policy== | ==Delete a Policy== | ||
| + | |||
| + | It’s possible to delete one or more policies simply clicking on the delete button. | ||
| + | |||
| + | [[Image:AuthPortlet_Delete_popup_check.png|413px|center|Auth Portlet Example Delete check a Policy]] | ||
| + | |||
| + | |||
| + | [[Image:AuthPortlet_Delete_popup.png|413px|center|Auth Portlet Delete a Policy]] | ||
Latest revision as of 15:18, 5 October 2016
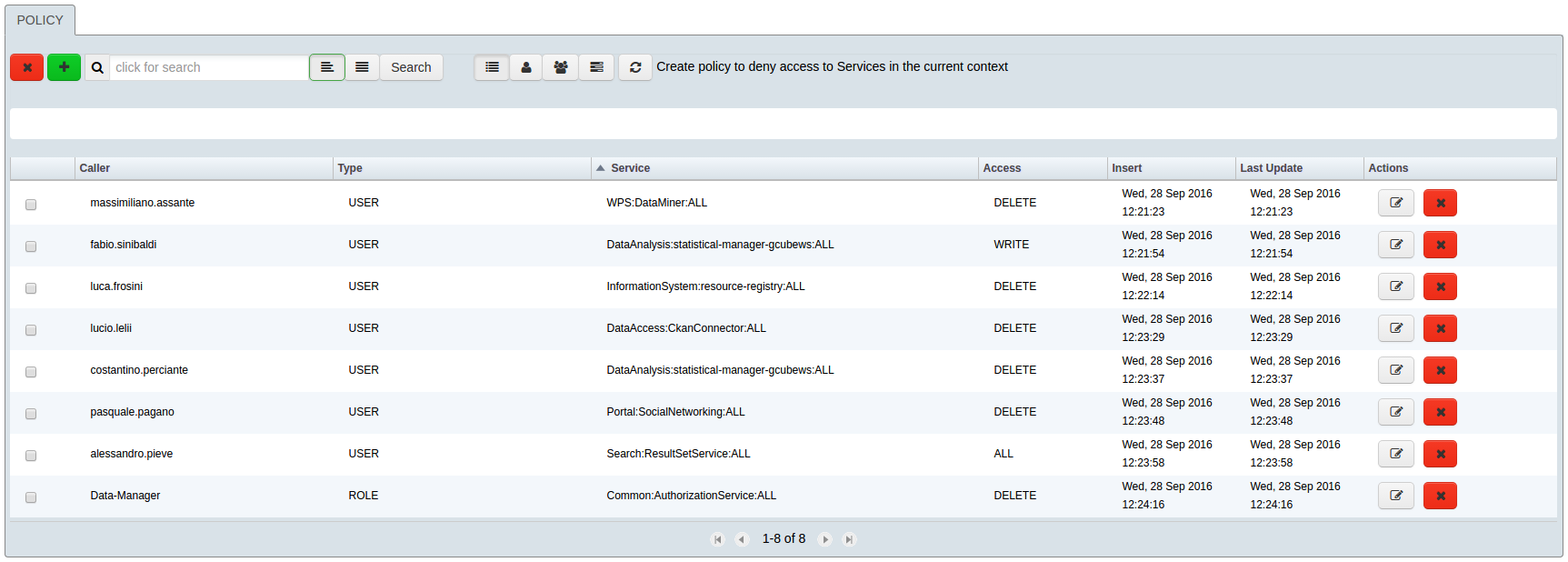
Introduction
With this portlet it’s possible to create a policy to deny access for a user or group of users to a service or group of services in a specific context.
Below it is shown the overall layout of the Auth Portlet
Every policy is consisting of:
- one or more Caller
- Service
- Access
The caller can be an User, a Role or a Service and you can insert one or more callers for each policy.
(The insertion of a policy with more callers results as more policy).
The service is specified as service class, service name and service id.
The access that we want to deny can be:
- All
- Access
- Delete
- Execute
- Write
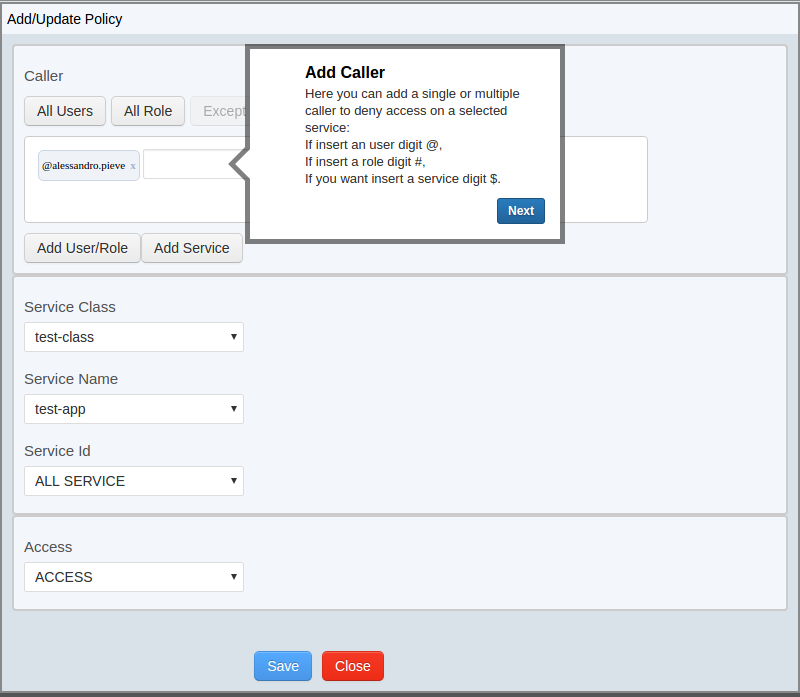
Insert/Modify a Policy
For insert a policy we can add one or more Caller, one service and access type.
The insertion of a caller can be made with an autocomplete writing in the input, or clicking the button Add User role or add service, that opens a pop-up to insert more things.
We can create a policy that inserts all users or all role with the specific button “All Users” or “All Role”
The insertion of a caller can be made with complete input text , or clicking button “Add User/ Role” or “Add Service” to open a pop up for multiple entry.
The insertion with an autocomplete can be made with the insertion of a first controlled character:
- if you insert a user, you can digit @ for see all users
- if you insert a role, you can digit # for see all roles
- if you want insert a service, you can digit $ for see all the services.
The selection of the service and the access type It’s done with a selected dropdown
We can insert a policy that allows the use of a service only to one or more caller, selecting the combination ALL Users/All role and Except.
In this case, the callers, entered in input text, are enabled to access a service.
For an existing policy, you can change only the service and the access type.
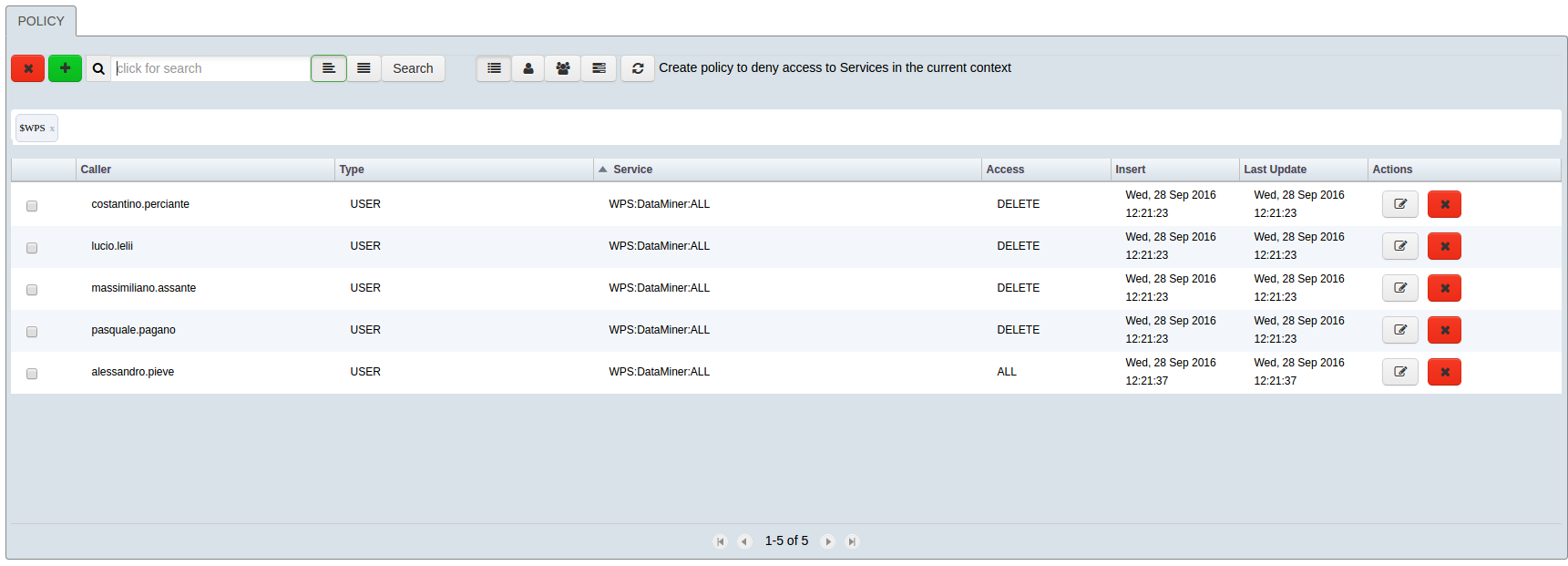
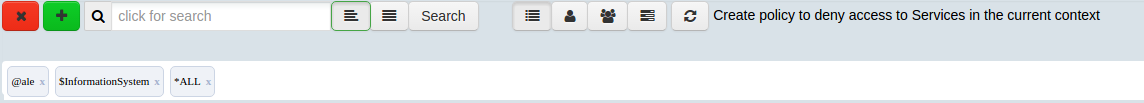
Search a Policy
It Is possible to search, filter and group by all policy.
If we want to search a caller, we can digit @ before inserting a name of the caller.
If we want to search a service, we can digit $ before inserting a name of the service.
And finally if we want to search an access, we can digit * before inserting a type of an access.
The filter can be incremental.
Over the filter we can organize a policy in caller type, for example user, role and service
Delete a Policy
It’s possible to delete one or more policies simply clicking on the delete button.